Computers Are Typically Protected From Viruses by the Use of
CISA recommends that all computers and mobile devices on your home network run antivirus software. Configurable TDP-up is the average power in watts that the processor dissipates when operating at the Configurable TDP-up frequency under an Intel-defined high-complexity workload.
The use of Configurable TDP-up is typically executed by the system manufacturer to optimize power and performance.
. If you have a wireless network at home make sure its secure and encrypted. That means the original files and any backup copies are vulnerable to theft fires floods and other proximate dangers. Worms often spread using parts of an operating system that are automatic and invisible to the user.
Create long and unique passwords or passphrases for much greater resistance to this type of attack. Viruses and malware continue to evolve and often cybercriminals use the type that gives them the best return at that particular time. Most people keep their external hard drives close to their computers either right next to it or somewhere else in the home or office.
For example the text-to-speech reads out text and helps retired citizens suffering limited vision comfortably use technology. As the popularity of smartphones exploded beyond that of computers as personal devices so did hackers. This online solution is much more reliable and safer than a physical workstation or home PC.
Additionally be sure to enable automatic virus definition updates to. They are identified by network addresses and may. To ensure that your data is protected Rentec Direct is always reviewing the most recent security practices and making sure to be alert of any possible security threats that may be sweeping the nation.
Controlling who gets to read information. Data sharing capabilities are typically blocked. Preventing viruses and worms.
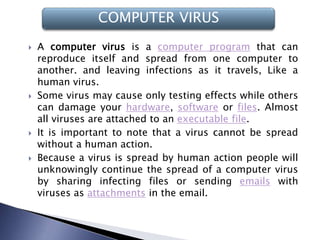
When people talk about getting a virus on their computer they usually mean some form of malwareit could be a virus computer worm Trojan ransomware or some other harmful thing. Assuring that authorized users have. Home PC or workstation.
DDoS attacks typically use botnets which are computers or other devices that have been infected by malware and are now under the control of the hacker. All Post Office broadband customers get to try SAFE for FREE for 6 months no card details taken up-front. If youre using an external hard drive for backup the best way to make sure your files are protected from all major risks is to back up.
Many antivirus solutions are extremely easy to install and intuitive to use. F-Secure SAFE offers Virus Protection Banking Shopping Protection Browsing Protection and Parental Controls. Its main function is to infect other computers while remaining active on the infected system.
Hackers can also use these botnets for various other cybersecurity threats like data theft account takeover web content scraping and more. Use a firewall. While a traditional virus replicates itself while running viruses on mobile devices target weak points within your operating system for data-mining financial gain or to corrupt a network.
Keyloggers may also collect functionality allowing for stealthy capture and transmission of images and audiovideo from any connected devices. If you have to use the internet but dont have access to a secure network change your passwords immediately the next time you log into a secure network. It can automatically detect quarantine and remove various types of malware such as viruses worms and ransomware.
For total piece of mind we offer F-Secure SAFE which is a comprehensive internet security suite protecting up to 7 of your mobiles tablets and computers. Keep in mind that wireless routers typically arent secure by default you have to set this up yourself. These are computers tailor-made to be extremely user-friendly and simple to set up.
A good firewall will block connections from any already-installed botnet malware to its CC server or other devices on a P2P botnet. Some include features that make them a joy to use for seniors with impairments such as hearing or sight problems due to age. Organizations and people that use computers can describe their needs for information security and trust in systems in terms of three major requirements.
The nodes of a computer network may include or other specialised or general-purpose. The computers use common over to communicate with each other. They typically collect screenshots of the current window at scheduled intervals.
They might even allow attackers to collect documents that are printed on connected printers which can then be transmitted to a remote server or. Once a worm enters a system it immediately starts replicating itself infecting computers and networks that arent adequately protected. Some botnet malware will brute-force a password until it cracks.
These interconnections are made up of technologies based on physically wired optical and wireless radio-frequency methods that may be arranged in a variety of. Assuring that information and programs are changed only in a specified and authorized manner.
What Is A Computer Virus And How To Avoid Infection In 2022

Biological Viruses Versus Computer Viruses 2020 08 21 Mission Critical Magazine

What Is A Computer Virus Types Of Computer Viruses Updated 2020
Common Computer Viruses Malware How To Detect And Remove Them

What Is A Computer Virus And How To Avoid Infection In 2022

State Machine For Computer Virus Spreading Download Scientific Diagram

How Do I Protect My Computer From Viruses Arnold Consult

What Is A Computer Virus How Can You Protect Yourself
14 Different Types Of Computer Viruses As Of 2022 Rankred

What Is A Computer Virus How Can You Protect Yourself
9 Common Types Of Computer Viruses High Touch Technologies

What Are The Different Types Of Computer Viruses Uniserve It

Computer Viruses Philip And Luke Ppt Video Online Download

Welcome Anti Virus Prezentaciya Onlajn
What Is A Computer Virus Knowledgebase Ictea

What Are The Different Types Of Computer Viruses Uniserve It

What Is A Computer Virus How Can You Protect Yourself

Computer Virus Types Examples What Is A Computer Virus Video Lesson Transcript Study Com

Comments
Post a Comment